Crypto scammers stole over $17 billion in 2025. Americans alone lost $9.3 billion to crypto fraud in 2024, and only around 10% of stolen cryptocurrency is ever recovered. Ethereum users are targeted more than users of most other blockchains because ETH is the most widely used network for DeFi, NFTs and dApp transactions, and because interacting with those applications requires wallet connections and token approvals that create more attack opportunities than simply holding a coin. This guide covers the most common Ethereum scams, the red flags that almost always appear before someone loses money, how to protect your wallet, and what to do if you have already been targeted.
Why Ethereum users are targeted
Ethereum transactions are irreversible. Once ETH or any token leaves your wallet, no bank, no support team and no government agency can return it. Scammers operate in environments where reversals are impossible, which is why they concentrate so heavily on crypto users.

Beyond irreversibility, the Ethereum network requires users to interact with smart contracts, approve token spending limits and connect wallets to decentralised applications. Each of these interactions is an opportunity for a scammer to insert a malicious step. A user on a traditional bank platform has one attack surface: their login credentials. An Ethereum user on DeFi has dozens: wallet connections, token approvals, transaction signatures, bridge interactions and more. The underlying mechanism of how the Ethereum network processes these interactions is explained in the guide on how Ethereum works.
The most common Ethereum scams in 2025 and 2026
Scammers reuse the same core tactics with small variations. Learning the mechanics of each type makes them significantly easier to spot before any money moves.
Phishing scams
Phishing is the most widespread attack on Ethereum users. Scammers build fake websites that copy MetaMask, Uniswap, OpenSea, Coinbase and almost every other platform Ethereum users visit. The fake site looks identical to the original, down to the logo, layout and URL format. The domain is slightly different: a letter swapped, a number added, a hyphen inserted. Once you connect your wallet or enter your seed phrase on a phishing site, the scammer has everything needed to drain your wallet.
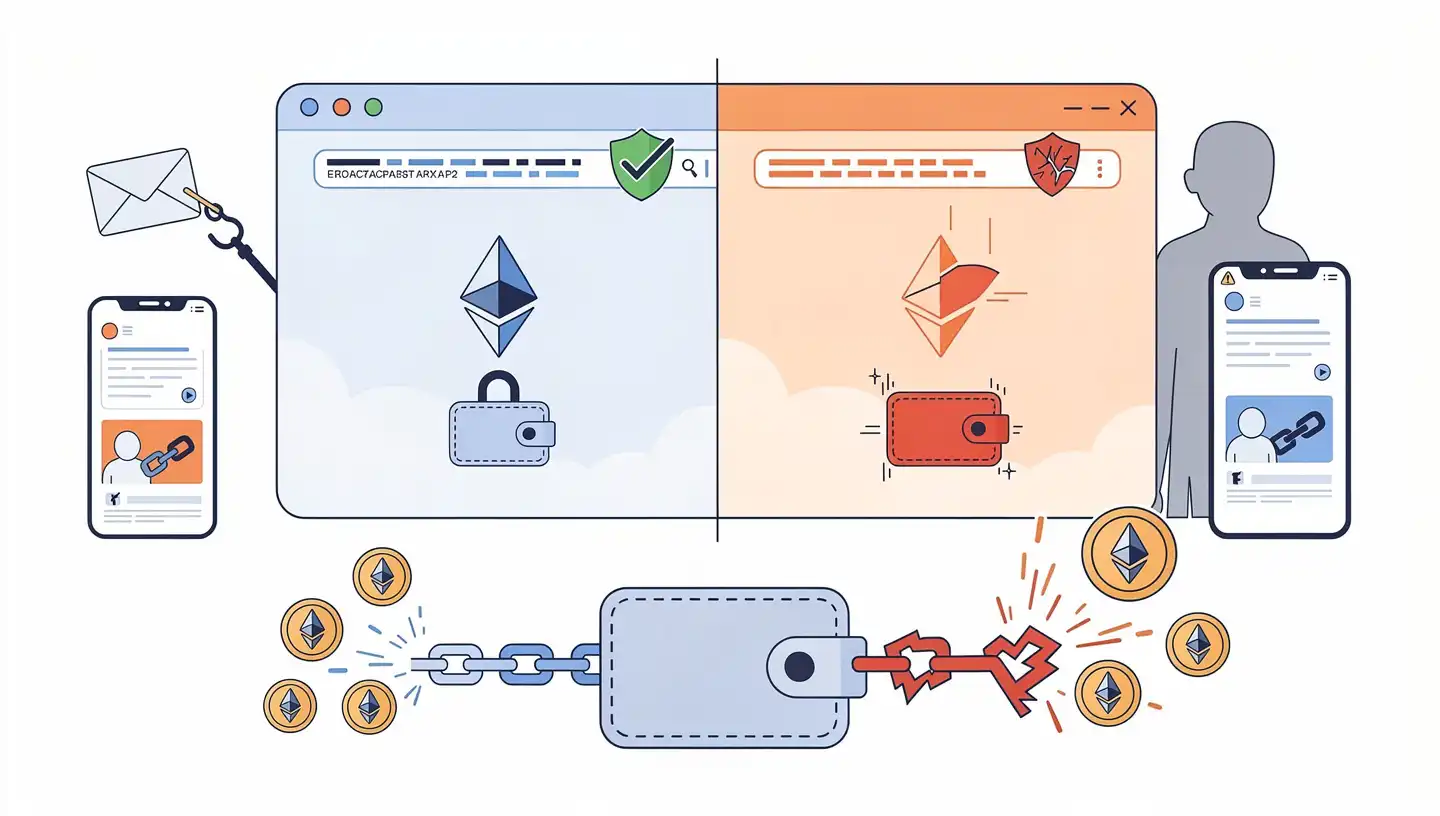
Phishing emails follow the same pattern. They impersonate support teams, claim your wallet is at risk or your account is being suspended, and direct you to a fake login page. One specific attack worth knowing about: scammers on Twitter and X can spoof the link preview system so that a malicious URL displays a preview showing a legitimate domain such as ethereum.org. The preview looks real but the link redirects to a different site entirely. Always check the address bar in your browser after clicking any link, not just the preview shown in a post or message. The guide on what Ethereum is covers why Ethereum has no central authority that would ever email you about account issues.
Giveaway scams
The giveaway scam is one of the oldest in crypto and still catches thousands of people each year. The format is always the same: send ETH to a specified address and receive double the amount back. This is sometimes called the 2-for-1 scam. No one has ever received doubled ETH back. Every person who has sent ETH to a giveaway address has lost their funds permanently.
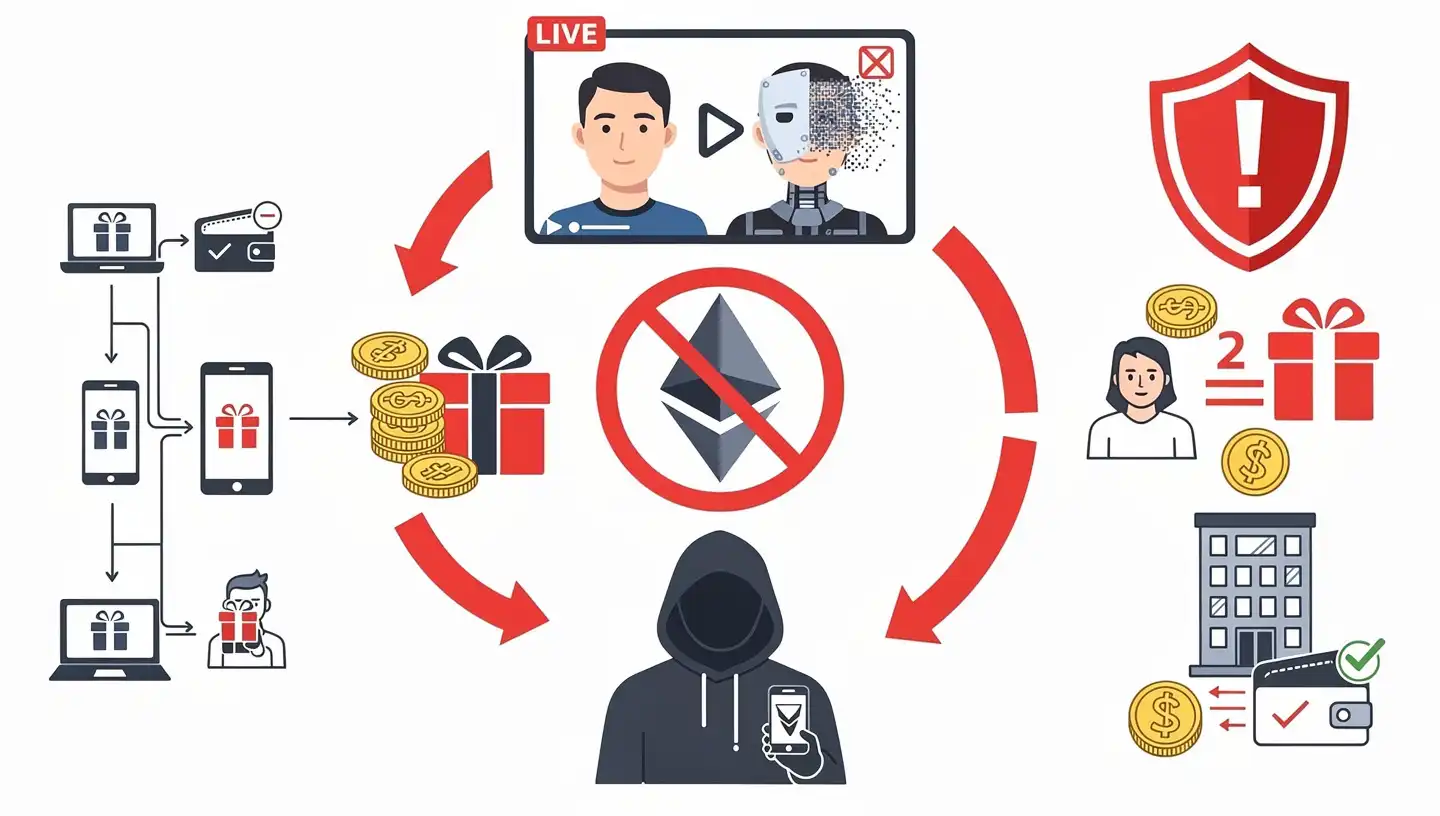
In 2025, AI deepfakes made giveaway scams more convincing than ever. Scammers create realistic video footage of Vitalik Buterin, Elon Musk or other well-known figures appearing to endorse a fake giveaway. These videos are livestreamed on YouTube to create the impression of a live event. AI-generated deepfakes increased by 1,400% in 2025. The rule is simple: no legitimate person, project or organisation will ever ask you to send ETH with a promise of returning more. If you see it, it is a scam.
Fake support scams
Fake support scammers monitor public channels on Discord and Telegram for users asking questions about MetaMask, Coinbase Wallet, Uniswap or any other Ethereum application. When they see someone post a support question, they send that person a private message claiming to be from the official support team. The profile looks legitimate: same name, same profile picture, same language style as the real team.
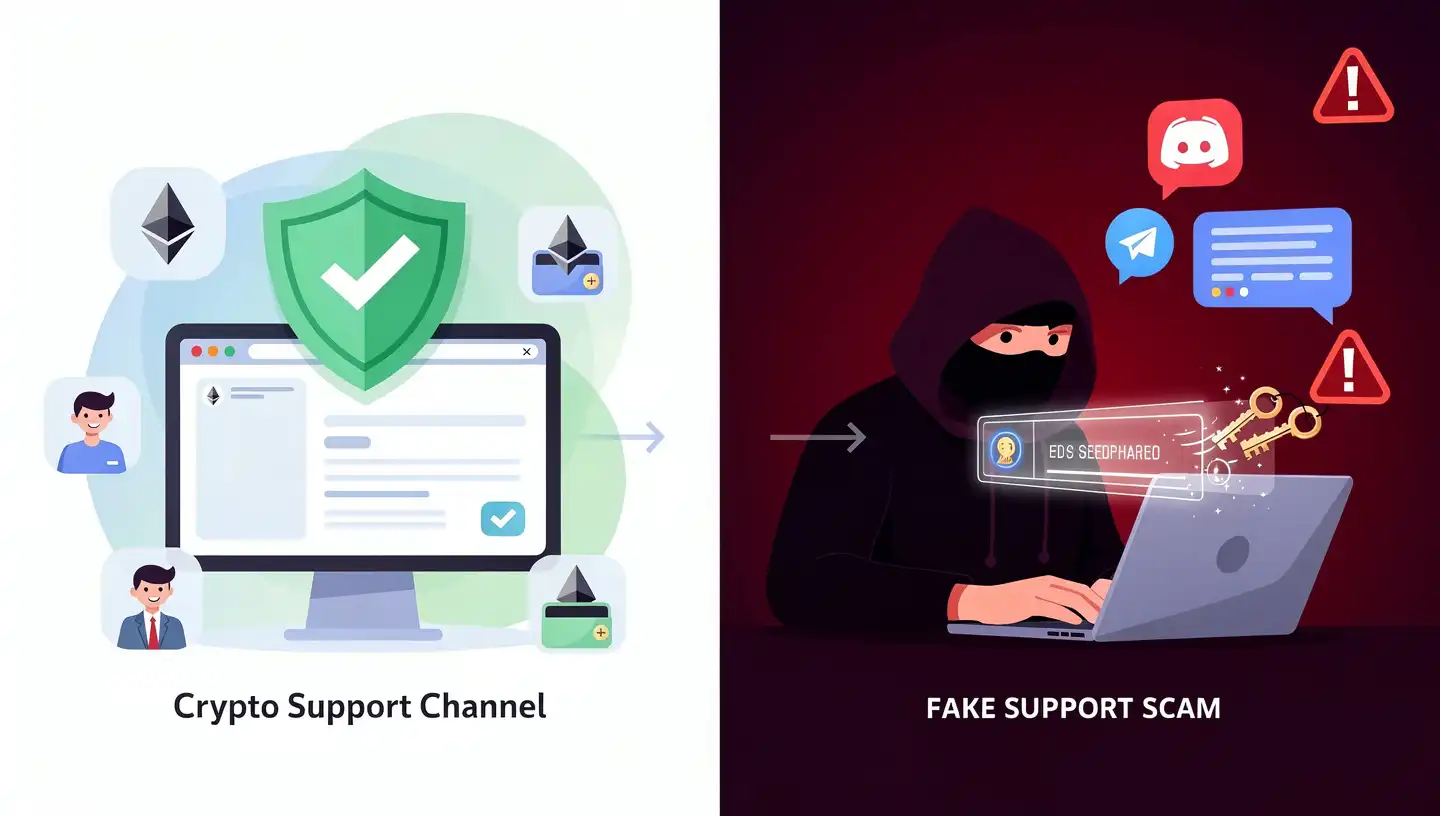
The support scam follows a predictable path. The fake support agent builds trust by asking a few generic troubleshooting questions, then steers the conversation toward asking for your seed phrase or private key, or directs you to a phishing site where you are asked to verify your wallet. Real support teams for Ethereum wallets and applications never contact users through direct messages on Discord or Telegram. Official support exists only through verified channels listed on the official website. If someone contacts you through DM offering help you did not request, treat it as a scam regardless of how legitimate the profile looks.
Rug pulls and honeypot tokens
A rug pull happens when a developer launches a token on a decentralised exchange, attracts buyers, and then removes all the liquidity from the trading pool and disappears. The token price collapses immediately. Investors are left holding a coin worth nothing that they can no longer sell because there is no liquidity to sell into. Rug pull losses from new tokens reached $900 million in 2025.

A honeypot token is a variation where the smart contract is written so that buyers can purchase the token but the sell function is blocked. You watch the price rise and cannot exit. You are trapped. Both rug pulls and honeypots are common on Ethereum-based decentralised exchanges. Before buying any token you found through social media or an unsolicited message, check the contract address on TokenSniffer or De.Fi Scanner. These tools flag missing sell functions, concentrated holder lists and unlocked liquidity pools. The gas fees involved in token trading on Ethereum are covered in the guide on Ethereum gas fees.
Pig butchering scams
Pig butchering is the name given to a long-form fraud that starts with relationship building and ends with financial devastation. The term describes how scammers fatten victims with trust before slaughtering them financially. The scammer initiates contact through a dating app, WhatsApp, Instagram or LinkedIn, often posing as a successful professional or romantic interest. The relationship develops over weeks or months through regular messages.
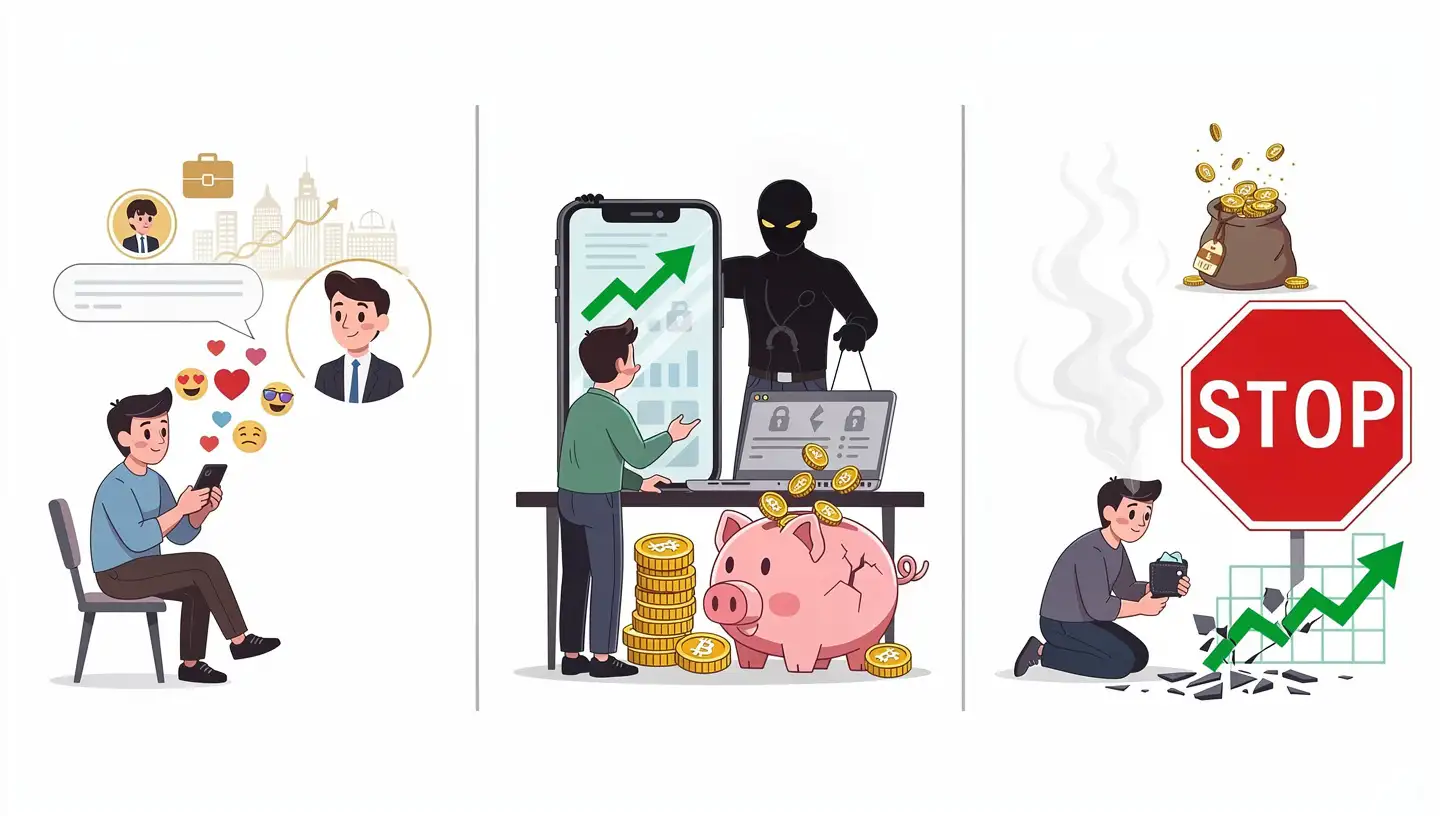
Once trust is established, the scammer introduces a cryptocurrency investment opportunity, often framing it as something they personally benefit from and want to share. They show you a professional-looking investment dashboard with growing returns. When you invest, the dashboard shows increasing profits. When you try to withdraw, the platform invents fees, taxes or verification requirements. The money is gone. Pig butchering scams have stolen over $75 billion globally since 2020. The FBI identified and notified more than 4,300 victims in 2025 who had no idea they were being scammed. If someone you met online and did not previously know recommends a crypto investment platform, assume it is a scam.
Fake airdrops and malicious token approvals
Fake airdrops are a specific risk for Ethereum users because of how token approvals work on the network. A scammer promotes a free token airdrop and directs users to a website to claim their tokens. Claiming requires connecting your wallet and signing a transaction. That transaction is not a simple receive. It contains a token approval granting an unlimited spending limit to the scammer contract. Once signed, the contract can pull all of your tokens from your wallet at any time, immediately or later.
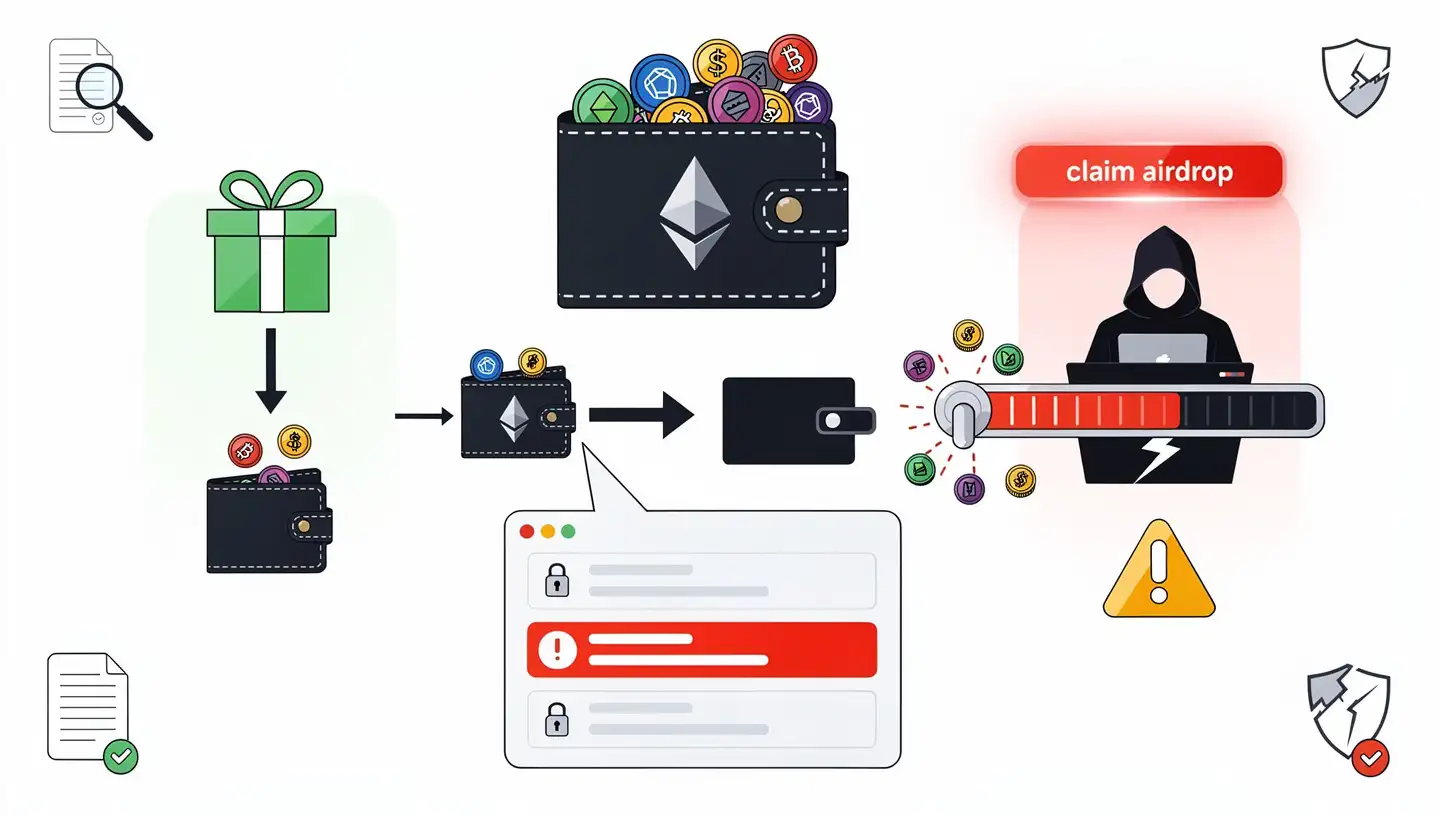
The attack works because most users do not read transaction details before confirming in MetaMask. The MetaMask popup shows a transaction requesting approval, and users click confirm without checking what the approval covers. A real airdrop does not require you to grant spending permissions. If claiming an airdrop requires you to sign an approval transaction, stop and read it carefully before proceeding. How smart contracts process these permission requests is explained in the guide on what smart contracts are.
Address poisoning
Address poisoning is an attack that emerged widely in 2025. A scammer sends a tiny transaction of zero value or a fraction of a cent to your wallet from an address that closely resembles one you use frequently. The fake address uses the same first four and last four characters as your genuine contact address but has different characters in the middle. The transaction shows up in your wallet history alongside your legitimate transactions.
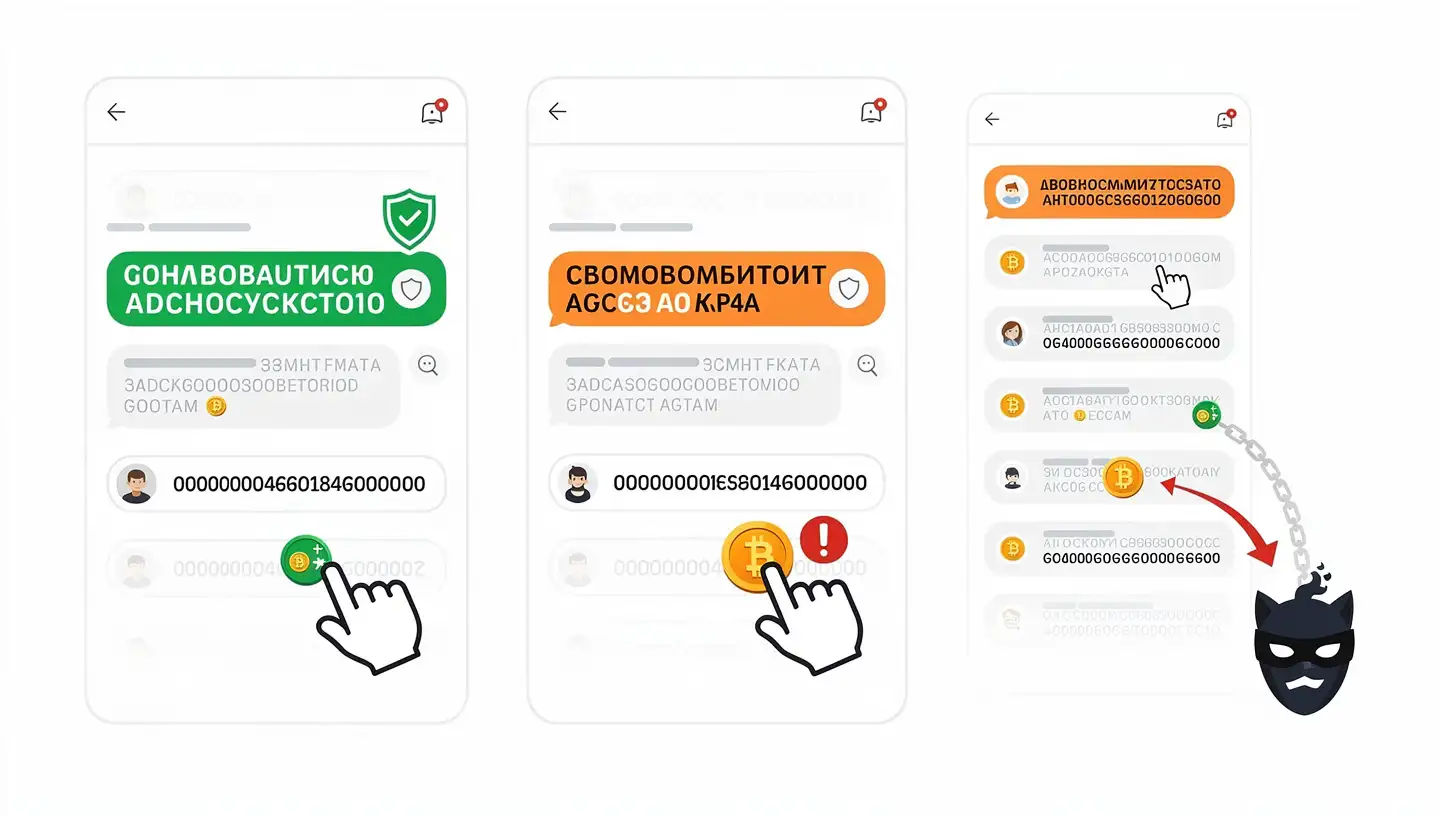
When you next need to send funds to that frequent contact, you open your transaction history, find the address and copy it. Without checking the full address, you copy the scammer version. Your funds go to the scammer. To avoid address poisoning: never copy wallet addresses from your transaction history. Always get the address directly from the recipient through a verified channel, or use a saved address book entry that you added manually. Before sending any significant amount, verify the complete 42-character address, not just the first and last four characters. How ETH transfers between wallets are processed is covered in the guide on how to transfer Ethereum.
Pump-and-dump schemes
Pump-and-dump schemes use coordinated social media campaigns to inflate the price of a low-value token. Scammers accumulate a large position in the token before promoting it aggressively on Telegram groups, X accounts and YouTube channels, often through paid influencers or bot networks. Retail buyers rush in as the price rises. When the price reaches the target level, the insiders sell their entire position into the buying surge. The price collapses and the buyers are left with a worthless token.

The 2025 Trump meme coin launch triggered over 700 copycat tokens attempting to impersonate it, each one a pump-and-dump aimed at buyers who could not distinguish the real project from the fakes. The warning signs are consistent: a sudden price spike with no fundamental news, promotion from anonymous accounts, a sense of urgency to buy immediately, and a very short trading history. If you are seeing a token for the first time because of social media promotion and it has already risen sharply, you are most likely looking at a pump-and-dump in progress. The history of why Ethereum was built as an open network that anyone can launch tokens on is covered in the guide on who created Ethereum.
Red flags that almost always signal a scam
Across all scam types, the same warning signs appear repeatedly. If you encounter more than two of these red flags in the same situation, stop all interaction immediately.
- Guaranteed returns. No one can guarantee profits in crypto. Any offer promising fixed daily returns, doubling your ETH or guaranteed yields is a scam.
- Urgency. Phrases like “only 2 hours left”, “limited spots”, “act before it is too late” are pressure tactics designed to stop you from thinking or researching.
- Unsolicited contact. Someone messages you first through DM with an investment opportunity, a job offer or a support request you did not initiate.
- Requests for your seed phrase or private key. No legitimate service, support agent or person ever needs these. If asked, end the conversation.
- Requests for remote access to your computer. No real support team needs to access your screen or device to help with a crypto issue.
- Anonymous team with no verifiable identity. No LinkedIn profiles, no GitHub history, no real names anywhere.
- Missing or generic whitepaper. Copy-pasted text, vague roadmaps and no technical detail are consistent signs of a project that does not intend to build anything.
- No working product or code. A legitimate project has deployable code, a testnet or at minimum open-source repositories.
- Support only through DM. Official support always has a public channel: a help centre, a ticketing system or a verified Discord support channel, not a private message.
- Token you can buy but not sell. If you buy a token and cannot find a sell route, you are in a honeypot.
- Pressure to decide without research time. Legitimate investments and opportunities do not disappear in hours. Any offer that cannot wait for you to do research is designed to prevent you from doing it.
How to protect your Ethereum wallet
The most common thread across all Ethereum scam losses is not technical failure. It is a user action taken without enough verification. The security practices below address the specific points where most losses occur.
Never share your seed phrase or private key
Your seed phrase, also called the secret recovery phrase, is a sequence of 12 words that controls your entire wallet. Anyone who has these words can import your wallet on any device and drain every asset from every account in it. Your private key works the same way for individual accounts.
No legitimate service will ever ask for your seed phrase. Not MetaMask support. Not Coinbase support. Not Ethereum Foundation staff. Not a verification website. Not a recovery service. If any person, website, popup or email asks for your secret recovery phrase, it is a scam regardless of how legitimate the request looks.
Do not take screenshots of your seed phrase and do not photograph it. Screenshots and photos sync to cloud services such as Google Photos and iCloud automatically, which makes them accessible to hackers who gain access to your cloud account. Write the phrase on paper in the correct order and store it somewhere physically secure. For significant long-term holdings, stamping the phrase onto a metal plate provides protection against fire and water damage. The guide on how to set up MetaMask covers seed phrase storage in detail.
Use a hardware wallet for significant holdings
A hardware wallet such as a Ledger or Trezor stores your private key on a physical device that never connects to the internet. Even if your computer or phone is fully compromised by malware, the private key cannot be extracted because it never leaves the device. Transactions must be physically confirmed on the hardware wallet itself.
For any amount above $1,000 or for funds you intend to hold long-term, a hardware wallet is the most effective security measure available. MetaMask can be used as the interface for a connected Ledger or Trezor, giving you the familiar MetaMask experience with hardware-level key security. The cold wallet holds the keys and the hot wallet handles the interface. The proof-of-stake mechanism that validates transactions signed by these keys is explained in the guide on Ethereum proof of stake.
Check and revoke token approvals
Every time you interact with a DeFi protocol for the first time, it asks you to sign a token approval. This approval grants the protocol permission to spend a specific token from your wallet. The problem is that many approvals are set to unlimited by default, meaning the contract can pull any amount of that token at any point in the future, not just for the current transaction.
Old, unused token approvals are a significant risk. If a protocol you approved six months ago is later exploited or turns malicious, an unlimited spend limit allows the attacker to drain your wallet even though you have not interacted with the protocol recently. To check and remove these permissions, go to Revoke.cash, connect your wallet or paste your address, and review every active approval. Click Revoke next to any permission you no longer use. Always set a custom spend limit equal to the exact amount of a transaction rather than accepting unlimited approval when prompted by a protocol. Reviewing your approvals every few weeks removes exposure to old permissions before they can be exploited. How the Ethereum Virtual Machine processes these approval transactions is covered in the guide on the Ethereum Virtual Machine.
Read every transaction before you sign
MetaMask and every other Ethereum wallet shows the full details of a transaction before you confirm it. Most users click Confirm without reading what the transaction actually does. Scammers rely on this habit.
Before signing any transaction, look at the contract address it is interacting with. Verify that address against the official project website. Check what the transaction is requesting: is it an approval, a transfer, a function call? Check the amount. If the transaction is requesting an approval, check what the spend limit is set to. If you do not understand what a smart contract call does, do not sign it. An unsigned transaction costs you nothing. A signed malicious transaction can cost you everything. The guide on what ETH is explains why every transaction requires ETH as gas, which is the practical reason you should never run your wallet balance to zero.
Set the auto-lock timer and use a strong password
Your MetaMask password protects access to the extension on your specific device. Set a strong, unique password that you do not use for any other service. In MetaMask, go to Settings, select Advanced, and reduce the auto-lock timer to 5 or 15 minutes. The default is 60 minutes, which leaves your wallet accessible to anyone who sits at your machine while you are away.
Use two-factor authentication wherever available but avoid SMS-based 2FA for any crypto account. SIM swap attacks allow scammers to contact your mobile carrier, impersonate you, and transfer your phone number to their SIM card. They then intercept every SMS code sent to that number. Use an authenticator app such as Google Authenticator or Authy instead of SMS for all exchange and wallet-related accounts. The guide on how to stake Ethereum covers additional wallet connection security relevant to staking platforms.
How to verify if an Ethereum project is legitimate
Before investing in any token or connecting your wallet to any protocol, run through this checklist. It takes five minutes and eliminates the vast majority of scam projects.
- Get the contract address from CoinGecko or CoinMarketCap. Never use a contract address from a social media post, a DM or a Telegram group. Scammers paste fake contract addresses that look similar to the real one. The verified listing on CoinGecko or CoinMarketCap is the only reliable source.
- Check the contract on Etherscan. Open Etherscan.io and paste the contract address. Look for: verified source code (a project that hides its code is a red flag), active transaction history across many wallets, and a healthy distribution of holders. If the top 10 wallets hold 80% or more of the supply, insiders can dump and collapse the price at will.
- Verify the team. Search the project team names on LinkedIn and GitHub. Real developers have verifiable histories. Stock photos, empty LinkedIn profiles or names that return no results are warning signs. An anonymous team is not automatically a scam, but it raises the stakes for the other checks.
- Read the whitepaper. A generic whitepaper with vague language, no technical detail or text that appears in other project documents is a sign the team has no real plan. Legitimate projects explain their mechanism, tokenomics and development roadmap in specific terms.
- Check the community. Read the Discord and Reddit discussions around the project. Are users debating the technology and asking technical questions, or is every post promotional hype? Bot-generated communities are recognisable by uniformity of language, lack of critical questions and accounts that were created recently.
- Run the contract through TokenSniffer or De.Fi Scanner. These automated tools check contracts for honeypot functions, hidden mint functions, blacklist capabilities and other features that indicate a scam. Neither is perfect, but a failed scan on either tool is a strong reason to stay away.
What to do if you have been scammed
If you send ETH or tokens to a scammer, act quickly on the steps below. Speed matters because some losses can be partially limited if exchanges receive reports before funds are converted.
First, if you know the scammer used a centralised exchange to receive the funds, contact that exchange fraud department immediately with the receiving wallet address and the transaction hash. Some exchanges can freeze accounts pending investigation if contacted quickly enough.
Document everything before memories fade: the transaction hash from Etherscan, the scammer wallet address, all screenshots of conversations, the dates and times of every interaction, and any website URLs involved. This documentation is necessary for every report you file.
Report the scam to the relevant authorities:
- United States: FTC at reportfraud.ftc.gov and FBI Internet Crime Complaint Center at ic3.gov
- United Kingdom: Action Fraud at actionfraud.police.uk
- European Union: your local police and Europol through their online reporting portal
Track the stolen funds on Etherscan. Blockchain transactions are public, and you can follow the movement of your funds across wallets. This information is useful for reports and, in rare cases, helps investigators identify exchange accounts where funds were converted.
Do not pay anyone who offers to recover your stolen funds. Recovery scams specifically target people who have already been defrauded. A stranger contacts you through DM, claims to be a crypto recovery specialist, and offers to retrieve your stolen funds for an upfront fee. This is always a second scam. No one can reverse a confirmed blockchain transaction. Chainalysis documented cases in 2025 where already-victimised users lost an additional $100,000 or more to fake recovery services. If someone offers to recover your crypto for payment, ignore them completely. The guide on how to buy Ethereum covers using regulated platforms that have fraud reporting procedures.
FAQ
Can ETH transactions be reversed or refunded?
No. Ethereum transactions are irreversible once confirmed on the blockchain. There is no bank, payment processor or central authority that can reverse a transaction or issue a refund. If ETH or tokens leave your wallet to a scammer address, they are gone. This irreversibility is one of the main reasons scammers target crypto users. There is no chargeback mechanism. Only around 10% of stolen cryptocurrency is ever recovered, and most of that comes from exchange account freezes in cases where the scammer used a regulated platform to cash out.
How do I know if a MetaMask approval request is safe?
Before clicking Confirm on any approval in MetaMask, check three things. First, verify the contract address against the official project website, not a search result,, the official domain you bookmarked. Second, check what the approval is granting: is it a specific amount or unlimited? Unlimited approvals are rarely necessary and are always riskier. Third, if you do not understand what the approval does, do not sign it. You can always decline and research before returning to the transaction. A transaction you do not sign costs nothing.
What is the safest way to store Ethereum?
A hardware wallet such as a Ledger or Trezor provides the highest level of security for Ethereum storage. The private key is held offline on the device and never connects to the internet, so software-based attacks cannot extract it. For smaller amounts or frequent trading, a software wallet such as MetaMask is acceptable, but the seed phrase must be stored offline on paper or metal and never photographed or stored digitally. The worst storage option is leaving ETH on a centralised exchange indefinitely. Exchanges have been hacked, and exchange accounts are not equivalent to owning your own private key.
What happens if I accidentally share my seed phrase?
Act immediately. Move all your funds to a new wallet before the scammer does. Open a fresh MetaMask installation, create a brand new wallet with a new seed phrase, and transfer every asset from the compromised wallet to the new address as fast as possible. Do not send everything in one transaction if gas is high. Prioritise the largest holdings first. Once a seed phrase is known to anyone else, that wallet should be treated as permanently compromised. Do not use it for future transactions even after the immediate crisis is over.
How do I know if a token is a honeypot?
Run the token contract address through TokenSniffer or De.Fi Scanner before buying. These tools simulate buy and sell transactions against the contract and flag cases where the sell function is blocked, taxed at 100% or unavailable to regular wallets. You can also check the contract source code on Etherscan. Verified code can be read directly, while unverified code is itself a warning sign. If the top holders of a token are very few wallets, or if the liquidity pool is not locked, both are indicators of a potential rug pull or honeypot setup.
Are hardware wallets 100% safe?
Hardware wallets eliminate the most common attack vectors by keeping private keys offline. They are not 100% safe because the human using them can still make mistakes. If you connect a hardware wallet to a phishing site and sign a malicious transaction, the transaction is executed even though your private key stayed on the device. A hardware wallet confirms what you approve, not whether you should approve it. The device protects your key. Your judgment protects you from approving bad transactions in the first place.
What is address poisoning and how do I avoid it?
Address poisoning is an attack where a scammer sends a tiny transaction to your wallet from an address that looks nearly identical to one you regularly send funds to. The fake address matches the first and last four characters of the real address. When you copy an address from your transaction history for a future transfer, you may accidentally copy the fake one. To avoid it, never copy addresses from your transaction history. Always get the recipient address directly from them through a verified channel, add frequently used addresses to your wallet address book, and verify the complete 42-character address before sending any amount.
What should I do immediately if I think I am being scammed?
Stop all transactions and do not send any more funds. Do not let urgency pressure you into acting before you can verify. Disconnect your wallet from any site you suspect is malicious through MetaMask Settings under Connected Sites. Go to Revoke.cash and revoke any recent approvals you signed on suspicious sites. If funds have already moved, note the transaction hash from Etherscan, document everything and contact the receiving exchange fraud department if you can identify which platform received the funds. Report the scam to the FTC, FBI IC3 or your local equivalent. Do not pay anyone who contacts you claiming they can recover your funds. The guide on how to sell Ethereum covers using regulated exchanges, which have fraud reporting processes for exactly these situations.









